by threshold | Jan 22, 2026 | Creative, Design, Digital Marketing, General, Marketing
When Deborah Hayes Advertising came to Threshold, the brief was clear: design a website for Maxwell Downtown Brooklyn that feels as refined and intentional as the building itself. Maxwell is a 40-story boutique-inspired residential tower in the heart of Brooklyn, where modern living blends creativity, community, and ease. The website needed to reflect that ethos while driving engagement and conversions.
the problem.
Luxury residential websites often feel corporate, overly dense, or disconnected from the lifestyle they promise. Maxwell required something different: a digital presence that feels curated rather than commercial, sophisticated without being stiff, and elevated yet approachable. The challenge was balancing strong visual storytelling with clarity, usability, and leasing performance across devices.
the dream.
We envisioned a website that doesn’t just show Maxwell’s lifestyle—it feels like it. Elegant without excess. Intentional without artifice. Distinctly Brooklyn. The goal was to translate Maxwell’s identity into a calm, editorial digital experience that invites exploration and mirrors the residence’s quiet confidence.
the strategy.
website design.
The visual concept was inspired by effortless sophistication—timeless, confident, and approachable. This guided a restrained visual language rooted in refined typography, a carefully curated color palette, and art-forward photography. Content pacing and generous white space allow the site to breathe, creating a calm browsing experience that reflects the building’s design sensibility.
website development.
User experience guided every technical decision. Clean navigation and a clear content hierarchy help visitors move seamlessly from residences to amenities to lifestyle storytelling. The responsive framework ensures a cohesive experience on desktop, tablet, and mobile. Interactive features—including an embedded virtual tour, refined animations, and real-time pricing and availability—engage visitors while maintaining simplicity. Strategically placed calls to action, such as Schedule a Tour and View Availability, support conversion goals and connect directly to the leasing process.
the results.
The Maxwell Downtown Brooklyn website delivers a sophisticated, user-first digital presence that reflects contemporary urban living—where modern luxury meets creativity, community, and ease. A strong conceptual foundation and meticulous execution elevate the brand while remaining intuitive and performance-driven. The work was recognized with a Gold Davey Award for Website Design, celebrating excellence in digital storytelling and user experience.
Read the full Maxwell Downtown Brooklyn website Case Study.

by threshold | Jun 6, 2024 | Creative, Design, Digital Marketing, General, Marketing
Yankee Mattress Company was looking for a revamp to its branding along with a new e-commerce website. They needed a more focused approach to their target market, with stronger messaging and values that elevated their branding to the same level as their high-quality mattresses.
Threshold wanted to position Yankee Mattress as more than a retail store, but an employee-owned company that’s invested in their customer’s quality of life.
our approach.
new brand positioning & naming.
Following extensive market and customer research, Threshold created two brand concepts for the client to choose from, both with a core purpose, messaging, tagline, brand voice, and visuals. Each concept brought the brand to a more modern place, differentiating it from competitors by highlighting the craftsmanship that goes into their mattresses.
a new brand look & feel.
The brand’s new messaging needed a new logo, brand guidelines, stationary, photography, apparel design, and more. We chose to design this brand with a logo font that spoke to handmade craftsmanship and a subtle mattress icon that would become a recognizable brand statement.
a killer e-commerce website.
Yankee Mattress’ previous website didn’t allow for a streamlined online ordering experience. Our website design included easily navigable shopping categories as well as detailed shop pages. Each mattress product page included custom graphic designs that detailed each section of the mattress materials, making it easy for customers to browse and select the mattress best suited for them.
We designed this website to mimic the in-store experience customers have, providing them with clear information so they could make informed decisions.
we love results.
The final brand not only connects better with the target audience, but it feels timeless and elevated. Each aspect of the brand ties in seamlessly with the next, inspiring the company’s employee-owners and ensuring the quality of the mattresses is felt within the quality of the branding.
One Year Post Website Launch (April 2023-March 2024):
- 446 New Users
- 7% Increase in Engagement Rate
- A 7% Reduction in Bounce Rate
before you go.
Yankee Mattress Company can now confidently say they’re crafting comfort for amazing sleep and better days. See the case study for a full look at the transformation our THeam created for them – and what we can do for you, next.
Let’s propel you forward too! Your place for your every marketing need, with us you can go a la carte or take all the carts. Talk to a Marketing Specialist today.

by threshold | Apr 10, 2024 | General
 Michael Pratt
Michael Pratt
In the ever-evolving landscape of digital marketing, businesses are increasingly recognizing the profound impact of sustainability on their online success. Beyond mere aesthetics and functionality, sustainable web design stands as a beacon of eco-conscious innovation, promising not only higher site traffic and conversions but also a brighter, greener future. Let’s explore how prioritizing sustainability in web design can catalyze remarkable growth for businesses while championing environmental stewardship.
elevating user experience with sustainable practices.
Sustainability isn’t just about reducing carbon footprints; it’s about enhancing every aspect of the user journey. By embracing minimalist layouts, optimizing code for efficiency, and prioritizing renewable resources, sustainable web design fosters an immersive user experience that resonates deeply with eco-conscious consumers. When visitors encounter a website that reflects their values of sustainability, they’re not just browsing – they’re engaging with a brand that speaks their language.
climbing the ranks with eco-friendly optimization.
Search engines have become gatekeepers of the digital realm, and sustainability is increasingly becoming a key criterion for ranking. Websites that load quickly, adapt seamlessly across devices, and prioritize energy-efficient hosting solutions are rewarded with higher visibility in search engine results. Sustainable web design isn’t just about pleasing algorithms; it’s about forging a symbiotic relationship with the environment while ascending the ranks of digital prominence.
empowering mobile users through green innovation.
In a world where smartphones reign supreme, sustainable web design ensures that no user is left behind. By crafting mobile-responsive experiences that conserve resources and minimize energy consumption, businesses can empower users to engage with their brands anytime, anywhere. Sustainable web design isn’t just about adapting to mobile devices; it’s about empowering a mobile generation to make conscious choices that resonate with the planet.
reducing bounce rates with sustainable speed.
Every wasted second is a missed opportunity in the digital realm. Sustainable web design prioritizes speed, efficiency, and optimization to minimize bounce rates and maximize conversions. By streamlining navigation, compressing images, and leveraging caching techniques, businesses can create websites that load in the blink of an eye, captivating visitors and inspiring them to explore further.
cultivating a reputation rooted in sustainability.
In a world where brands are under constant scrutiny, sustainability isn’t just a buzzword – it’s a badge of honor. By embracing sustainable web design, businesses signal their commitment to environmental stewardship, earning the trust and loyalty of eco-conscious consumers. A website that embodies sustainability isn’t just a digital storefront; it’s a testament to a brand’s values and a beacon of inspiration for a greener tomorrow.
to wrap things up.
In the quest for digital dominance, sustainability isn’t just an afterthought – it’s the cornerstone of long-term success. By embracing eco-conscious web design practices, businesses can drive higher site traffic, boost conversions, and forge deeper connections with consumers who share their commitment to the planet. In the digital frontier of tomorrow, sustainability isn’t just an option – it’s the path to prosperity and progress.
before you go.
For more tips and information about marketing your everything, take a look at the rest of our blogs, right here on our website!
You can also subscribe to our email newsletter (it’s got some great stuff), and follow us on Instagram, Facebook, or LinkedIn!
about the author.
Michael is the WordPress Designer and Developer here at Threshold.
As a seasoned UI/UX & Web Designer based in Chicago, Michael brings over six years of experience to Threshold’s creative team, creating top-notch web designs, applications, and user-friendly interfaces with marketing at the forefront.
His love for pushing boundaries and collaborating with others on new projects is matched only by his commitment to delivering outstanding work. He always takes a holistic approach to design, expertly weaving traditional techniques with the latest advancements to bring exceptional results to life.
When he’s not killing the creative game, here are some fun facts about how Michael enjoys his free time:
- I recently lived on the West Coast for 3 years and got to hike some of the most incredible mountains! Mount Rainier and Mount St. Helens to name a few.
- I studied herbalism, ayurveda, and alternative healing. Paired with basic nutrition knowledge, I’ve been able to help friends and family live a better quality of life.
- I did an internship as a videographer with Creature Skateboards and got to meet several professional skateboarders, filming for promos and events.
- I have family located in Athens, Greece and it is one of my favorite places to visit!
- I recently started learning Judo martial arts and it is an exciting endeavor along with my many other fitness goals!
by threshold | Apr 4, 2024 | Creative, Design, Digital Marketing, General, Marketing, Tech/Web
PeakMade Real Estate came to us needing a platform that allowed for a more streamlined approach to websites across their portfolio and understood that the user journey is different across their various markets.
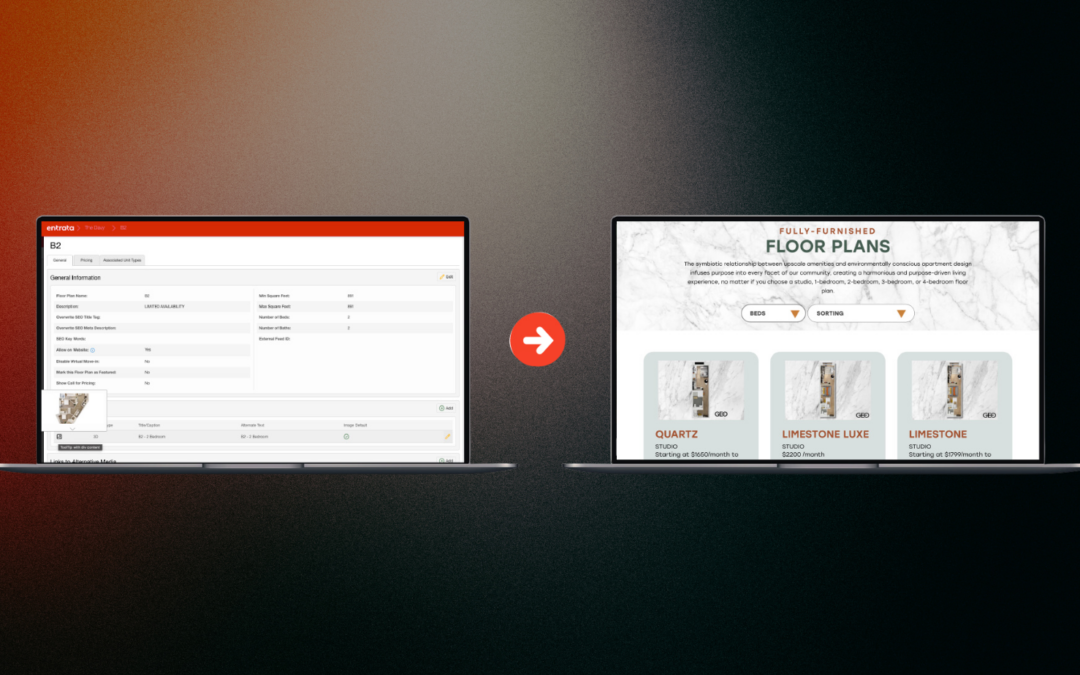
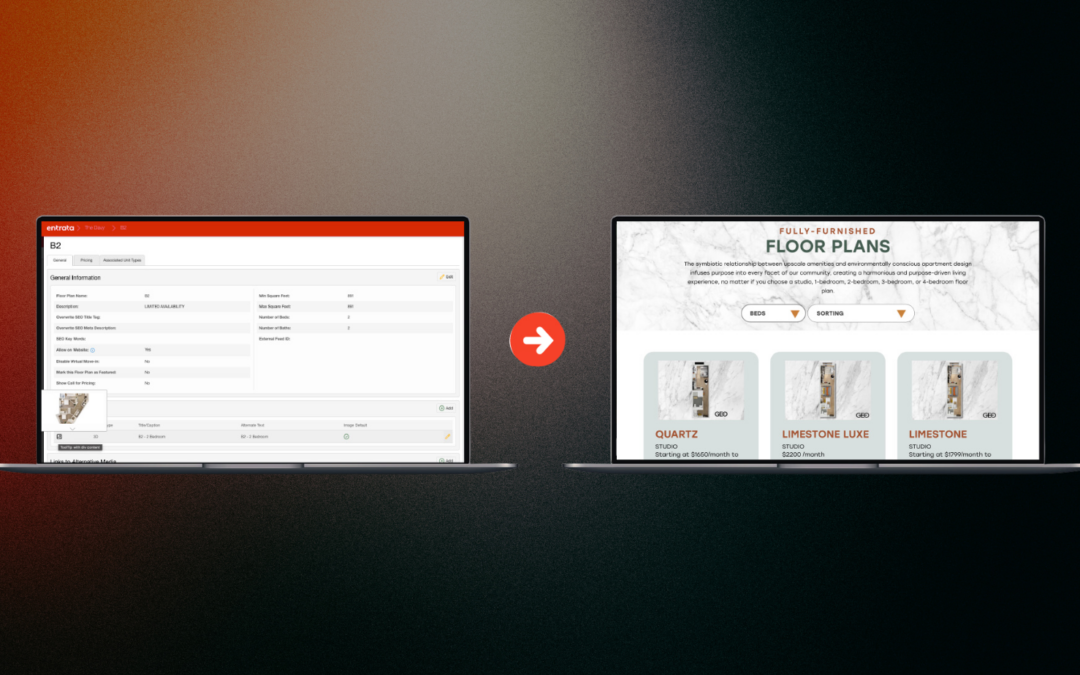
So we did what we do best, implementing website templates optimized for Peak’s audiences that have significantly reduced website development time and include a custom Entrata integration that converts better than any leading property management software on the market.
when we say best, we mean it.
We wanted to not only simplify website development but also provide PeakMade’s portfolio with a marketing tool that amplified lead generation. Each template design was to be innovative, with thoughtful movement of content to engage the viewer while not overwhelming them.
Our adaptable designs show an immediate improvement in conversion rates in the PeakMade portfolio, with lower costs to acquire leads when comparing the performance of their pay-per-click campaigns year-over-year from pre-templated Threshold websites to post.
Claremont Collegiate Apartments in Claremont, CA. saw:
- A 213% increase in conversion rate
- A 65% decrease in cost per conversion
University Gateway in Los Angeles, CA. saw:
- A 1,607% increase in conversion rate
- An 83% decrease in cost per conversion
Impressed? See more for yourself.
a custom integration? you got it.
Up until now, Entrata’s API allowed only floor plan pricing to be pulled into websites. Threshold built a custom integration for Entrata that retrieves several data points such as property floor plan details, availability, pricing, specials, and general property promotions, leveraging automation and increasing website accuracy and sustainability.
Our custom PeakMade templated designs and integration go far beyond the current property website capabilities, allowing property managers to:
- Set a custom pricing label option for floor plans with the ability to customize individual floor plan specials and floor plan name options
- Introduce a rent pricing override option for quick and easy discounted pricing updates when needed
- Create specials and offers that automatically remove themselves from the website when they expire
What does this mean for the property management teams?
- Information refreshes automatically
- No more spending precious hours updating leasing information or submitting requests through Threshold
- User-friendly back-end access to make certain edits on their own, without having to wait the standard 24-72 hour agency request turnaround time
- Focus on leasing and know that the property’s website is accurate and up-to-date
we love results.
How fast do you need a website? Because Threshold and PeakMade launched several of these custom website templates in only 26 business days. But the results don’t stop there.
When switching their property websites from Entrata templated designs to Threshold’s customized solution, PeakMade saw some dramatic improvements.
Taking a sample of 10 property websites from 2022-2023, the PeakMade team saw the following changes:
- Average time on a website increased by 33 seconds across all sites
- An engagement rate increase of 7.74%
- A goal conversion rate increase of 77.61%
before you go.
The 411? Using the Entrata designs and limited plugins was costing PeakMade properties conversions. Their new Threshold website templates look better than the previous property websites and provide a much-improved user experience that’s consistently resulting in better website engagement and higher lease numbers.
Let’s propel you forward. Your place for your every marketing need, with us you can go a la carte or take all the carts. Talk to a Marketing Specialist today.

by threshold | Sep 14, 2023 | Digital Marketing, General, Marketing, Tech/Web, Thought Leadership
 Michael Pratt
Michael Pratt
How do you stand out in a sea of competition? By guiding your audience through a killer experience.
Effective UI/UX design is increasingly recognized as a cornerstone of successful digital marketing endeavors. And within the real estate industry, where visual appeal and user engagement are paramount, crafting immersive digital experiences is crucial.
We’re sharing the secret sauce to engaging your audience below, so don’t click away just yet!
first impressions. they’re kind of a big deal.
UI, the visual layout and aesthetics, and UX, the overall user experience, profoundly impact initial impressions.
In real estate marketing, where potential residents will turn away if properties aren’t presented in the best light, a well-designed and intuitive website fosters trust and encourages visitors to go down a rabbit hole of site exploring.
make every visitor a navigator pro.
In real estate marketing, streamlined navigation is, well, kind of essential. Intuitive UI/UX design ensures potential buyers can effortlessly browse listings, view property details, and access contact information.
A seamless navigation experience enhances user satisfaction and encourages conversion. Cha-ching!
tap into those emotions.
Effective UI/UX evokes emotional connections. High-quality imagery, immersive virtual tours, and engaging property descriptions amplify the emotional resonance of a property. What does this do? Lots.
Emotional engagement strengthens branding and increases the likelihood of prospective buyers reaching out.
not local? not a problem.
Navigating a real estate website should mirror the ease of visiting a property in person. Effective UI/UX ensures intuitive property categorization, filtering, and detailed property information presentation.
So even if your prospects aren’t local to the property location, this seamless exploration process enhances their satisfaction and encourages extended engagement.
get people inquiring about you.
UI/UX design influences users’ interaction with contact forms, chatbots, and other communication channels. Streamlined interfaces facilitate inquiries and foster trust, ultimately translating into increased lead generation.
to wrap it all up.
The potency of UI/UX design in real estate marketing cannot be underestimated. As online interactions increasingly shape buyers’ decisions, a strategic focus on immersive, user-centric experiences is paramount.
Don’t be discouraged! Threshold is an expert in this domain, employing innovative UI/UX strategies that truly transform real estate marketing.
By cultivating emotional engagement, streamlining interactions, and delivering personalized experiences, we underscore the potential of UI/UX to redefine success in the dynamic landscape of real estate marketing.






 Michael Pratt
Michael Pratt